🧠 AuditSec Intel™ 1070
“The Vendor Trust Fallacy: Why Third-Party Access Became the Fastest Breach Path in 2025”
🔍 Introduction — Trust Was Granted. Verification Wasn’t.
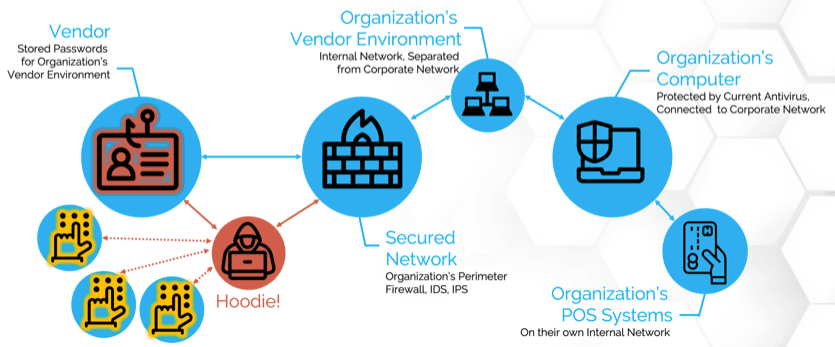
In 2025, attackers didn’t break firewalls.
They logged in.
They didn’t exploit zero-days.
They used valid vendor credentials.
Across breach investigations, one truth emerged:
Vendors were trusted by policy — but forgotten by practice.
CISORadar calls this the Vendor Trust Fallacy.
⚠️ 2025 Breach Pattern — The Silent Vendor Entry
| Industry | Breach Vector | What Went Wrong | Dwell Time |
|---|---|---|---|
| BFSI | MSP Admin Access | No quarterly review | 147 days |
| Healthcare | SaaS Support Account | MFA bypass | 91 days |
| Retail | Logistics Partner VPN | Shared credentials | 183 days |
| Manufacturing | OT Vendor Access | No time-bound access | 221 days |
Key Insight:
Vendors entered legitimately — and stayed invisibly.
🧩 Ignored Control
ISO 27001 A.5.19 / A.5.21 / NIST AC-2 / SR-3
Third-Party Access Governance
| Control Area | Objective | Common Failure |
|---|---|---|
| Vendor Onboarding | Least privilege | Full access granted |
| Access Duration | Time-bound access | “Permanent temporary” |
| MFA Enforcement | Strong auth | Exempted vendors |
| Review Cadence | Quarterly validation | Annual or never |
| Ownership | Vendor sponsor | Nobody accountable |
| Offboarding | Revoke immediately | Contract ≠ access |
💬 CISORadar Observation:
“Organizations deboard vendors faster than they de-authorize them.”
🧠 CISORadar Control Test of the Week
Control Reference: ISO 27001 A.5.19 / NIST AC-2
Objective: Ensure vendor access is justified, limited, and continuously verified.
🔍 Test Steps
1️⃣ Inventory all vendor and partner identities
2️⃣ Map access to contracts and business purpose
3️⃣ Validate MFA enforcement for vendors
4️⃣ Identify shared or generic vendor accounts
5️⃣ Check last access vs contract validity
6️⃣ Validate sponsor ownership
7️⃣ Test emergency access expiry
8️⃣ Calculate Vendor Access Risk Index (VARI)
✅ Expected Outcomes
- 100% vendor access mapped to contracts
- No shared vendor credentials
- All vendor access time-bound
- Quarterly access attestation
- Automated offboarding
Suggested Tools:
IAM | PAM | ZTNA | CASB | CISORadar Vendor Access Lens
🧨 Real Case — “The Trusted Vendor Who Never Logged Out”
A SaaS support vendor retained admin access
11 months after contract termination.
Attackers reused old credentials.
No malware. No exploit. No alerts.
Impact: ₹2,400 Crore + regulatory penalties.
Lesson:
“Third-party access is insider access without loyalty.”
🚀 CISORadar Impact Model — Vendor Access Risk Index (VARI)
| Metric | Before CISORadar | After CISORadar |
|---|---|---|
| Vendor Access Visibility | Partial | Complete |
| MFA Coverage | 42% | 100% |
| Time-Bound Access | Rare | Enforced |
| Orphan Vendor Accounts | 38 | 0 |
| Audit Findings | High | Zero |
🧭 Leadership Takeaway
Zero Trust must apply to vendors first — not last.
Boards must stop asking:
❌ “Do vendors need access?”
And start asking:
✅ “Why do they still have it?”
CISORadar transforms vendor trust into governed assurance.
📩 Download
Vendor Access Audit Checklist + VARI Scorecard
(ISO 27001 / NIST AC-2)
Available inside the CISORadar Cyber Authority Community.
🔖 SEO Tags
#AuditSecIntel #ThirdPartyRisk #VendorAccess #ISO27001 #NISTAC2 #CISORadar #SupplyChainSecurity #ZeroTrust #DigitalTrust #AuditIntelligence