🧠 AuditSec Intel™ 1061 – “The Secrets Sprawl Crisis: How Hard-Coded Secrets Became the Silent Cloud Breach Vector in 2025”
🔍 Introduction — The Breach Nobody Logged
In 2025 breach investigations, one pattern kept repeating — silently:
No phishing.
No malware.
No alerts.
Just a valid token.
CISORadar incident reviews revealed:
👉 API keys hard-coded in code
👉 Secrets embedded in CI/CD pipelines
👉 Credentials stored in config files, scripts, and images
👉 Tokens never rotated — never monitored
Attackers didn’t steal credentials.
They found them already exposed.
CISORadar calls this: The Secrets Sprawl Crisis.
⚠️ 2025 Case Files — When Secrets Did the Damage
| Sector | Secret Type | Exposure Location | Impact |
|---|---|---|---|
| SaaS | API Keys | Git repo history | Tenant takeover |
| BFSI | DB Credentials | CI/CD pipeline | Data exfiltration |
| Healthcare | Service Tokens | App config files | PHI breach |
| Cloud Native | OAuth Secrets | Container images | Cloud account abuse |
| Retail | Webhooks | Hard-coded scripts | Payment fraud |
CISORadar Insight:
“Secrets weren’t breached —
they were left behind.”
🧩 Ignored Control: ISO 27001 A.8.24 / A.5.17 / NIST IA-5 — Secrets & Credential Lifecycle Management
| Control Area | Objective | Common Failure |
|---|---|---|
| Secret Storage | Centralize secrets | Secrets in code |
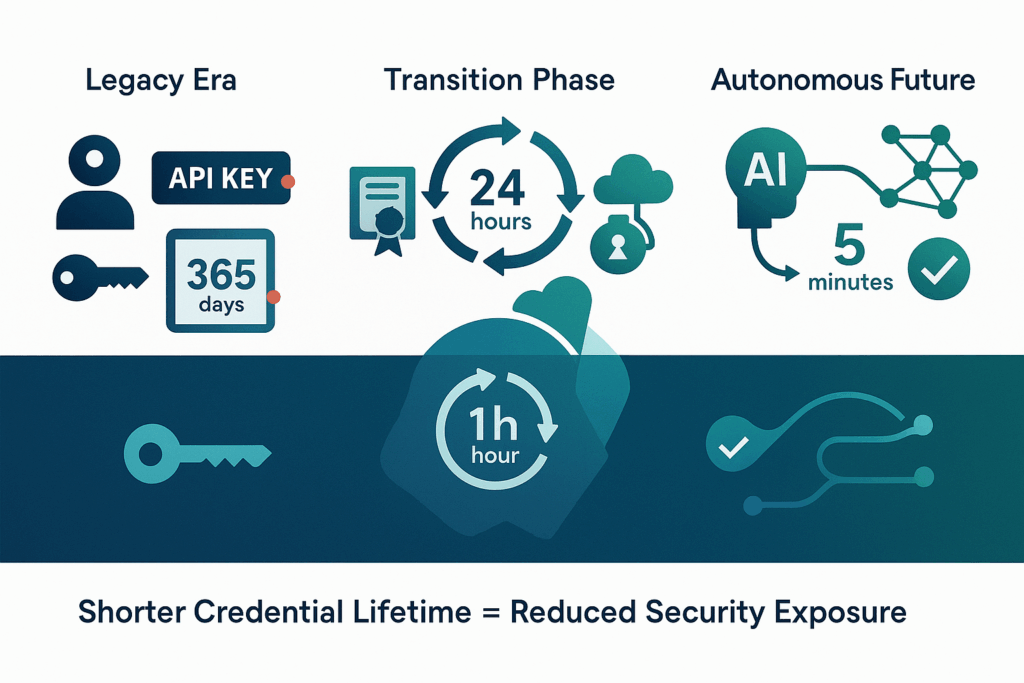
| Rotation | Limit secret lifetime | Never rotated |
| Scope | Least-privilege secrets | Over-scoped tokens |
| Visibility | Discover exposed secrets | No scanning |
| CI/CD | Protect pipelines | Plain-text variables |
| Revocation | Kill leaked secrets | No revoke process |
💬 CISORadar Observation:
“Passwords expire —
secrets quietly live forever.”
🧠 CISORadar Control Test of the Week
Control Reference: ISO 27001 A.8.24 / NIST IA-5
Objective: Identify, contain, and govern secrets before attackers do.
🔍 Test Steps
1️⃣ Scan repos, pipelines, and images for embedded secrets.
2️⃣ Inventory all application, service, and API credentials.
3️⃣ Identify secrets without rotation policies.
4️⃣ Review scope and permissions of secrets.
5️⃣ Validate centralized secret management usage.
6️⃣ Test revocation speed for exposed secrets.
7️⃣ Simulate leaked token abuse.
8️⃣ Generate CISORadar Secrets Exposure Index (SEI).
🔎 Expected Outcomes
✅ No secrets in code or images
✅ All secrets centrally managed
✅ Rotation enforced
✅ Scopes minimized
✅ Revocation tested and fast
Tools Suggested:
Secrets Manager | Vault | CI/CD Scanners | Repo Scanning | CISORadar Secrets Risk Lens
🧨 Real Case: The Forgotten Token
A developer committed a test API key — years ago.
Attackers found it in repo history.
It still worked.
Loss: ₹1,670 Crore.
Lesson:
“Secrets don’t forget —
attackers don’t need to guess.”
🚀 CISORadar Impact Model – Secrets Exposure Index (SEI)
| Metric | Before CISORadar | After CISORadar |
|---|---|---|
| Hard-Coded Secrets | Common | Eliminated |
| Secret Rotation | Rare | Enforced |
| Exposed Tokens | Unknown | Zero |
| Revocation Time | Days | Minutes |
| Secrets Visibility | Low | High |
🧭 Leadership Takeaway
“Zero Trust fails
when secrets trust forever.”
Boards must demand:
👉 Secrets inventory
👉 Rotation evidence
👉 CI/CD protection metrics
👉 Revocation speed SLAs
👉 Reduction in credential-based incidents
CISORadar turns invisible secrets into governed identity assets.
📩 Download
Secrets Governance Audit Checklist + SEI Scorecard
(ISO 27001 / NIST IA-5)
Available inside the CISORadar Cyber Authority Community.
🔗 Join Now → CISORadar Cyber Authority Community
🔖 SEO Tags
#AuditSecIntel #SecretsManagement #CredentialSecurity #APIKeys #ISO27001 #NISTIA5 #CloudSecurity #CISORadar #ZeroTrust #DevSecOps
Disclaimer: This post provides general information and is not tailored to any specific individual or entity. It includes only publicly available information for general awareness purposes. Do not warrant that this post is free from errors or omissions. Views are personal