🧠 AuditSec Intel™ 1065 – “The Machine Trust Explosion: How Over-Trusted Services Became the New Insider Threat in 2025”
🔍 Introduction — The Insider Wasn’t Human
In 2025 breach investigations, CISORadar uncovered a dangerous shift:
The most powerful identities
❌ were not employees
❌ were not admins
❌ were not vendors
They were machines.
Service accounts, workloads, APIs, bots, and AI agents were trusted more than people — and governed far less.
CISORadar calls this: The Machine Trust Explosion.
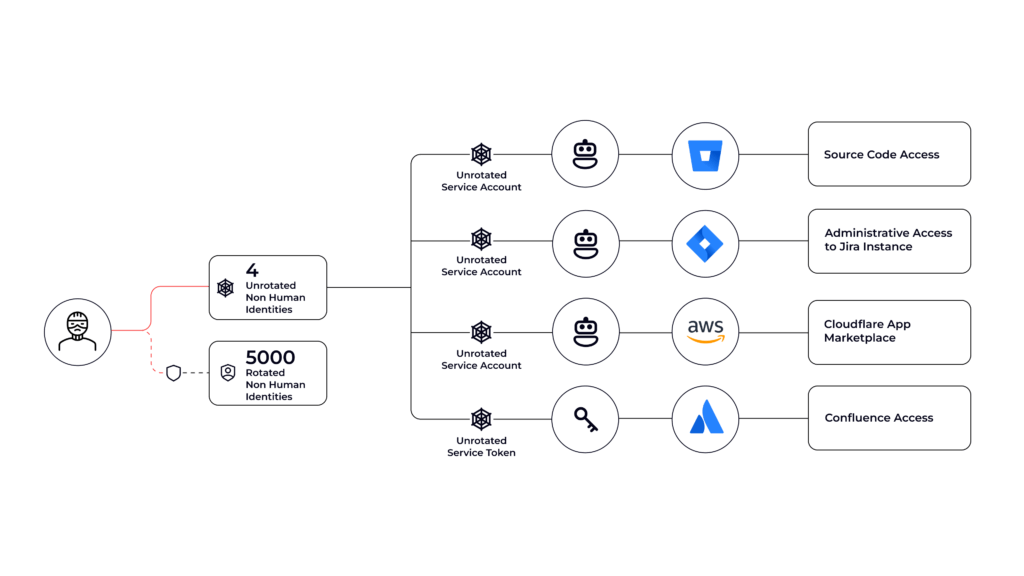
⚠️ 2025 Breach Pattern — When Machines Had Too Much Freedom
| Identity Type | Trust Model | Failure | Impact |
|---|---|---|---|
| Cloud service account | Implicit trust | No scope limits | Data exfiltration |
| Kubernetes workload | Flat service mesh | No identity enforcement | Lateral movement |
| API integration | Permanent token | No rotation | Account takeover |
| AI agent | Over-privileged | No guardrails | Unauthorized actions |
| Automation bot | Broad permissions | No audit trail | Control disablement |
CISORadar Insight:
“Machines became insiders —
without insider controls.”
🧩 Ignored Control: ISO 27001 A.5.18 / A.8.24 / NIST AC-2, IA-5 — Non-Human Identity Governance
| Control Area | Objective | Common Failure |
|---|---|---|
| Identity Inventory | Know all machine identities | Shadow service accounts |
| Scope Control | Least privilege | Wildcard permissions |
| Credential Lifecycle | Rotate & revoke | Static secrets |
| Authentication | Strong identity | Shared tokens |
| Monitoring | Observe behavior | Blind trust |
| Ownership | Assign accountability | No owner |
💬 CISORadar Observation:
“We rotated passwords —
but let machine identities live forever.”
🧠 CISORadar Control Test of the Week
Control Reference: ISO 27001 A.5.18 / NIST AC-2
Objective: Reduce machine trust to measurable, revocable access.
🔍 Test Steps
1️⃣ Inventory all non-human identities (APIs, workloads, bots, agents).
2️⃣ Identify identities without owners.
3️⃣ Review scopes and permissions.
4️⃣ Validate credential rotation and expiry.
5️⃣ Check service-to-service authentication.
6️⃣ Review machine activity logs.
7️⃣ Simulate compromised service account abuse.
8️⃣ Calculate Machine Trust Risk Index (MTRI).
🔎 Expected Outcomes
✅ All machine identities inventoried
✅ No shared or permanent secrets
✅ Scopes minimized
✅ Ownership assigned
✅ Abnormal machine behavior detectable
Tools Suggested:
IAM for Workloads | Service Mesh | Secrets Mgmt | Cloud IAM | CISORadar Machine Trust Lens
🧨 Real Case: “The API That Never Logged Out”
A service account created for testing.
Never rotated.
Never monitored.
Attackers found it.
Loss: ₹2,180 Crore.
Lesson:
“Machines don’t make mistakes —
humans make them permanent.”
🚀 CISORadar Impact Model – Machine Trust Risk Index (MTRI)
| Metric | Before CISORadar | After CISORadar |
|---|---|---|
| Machine Identity Inventory | Partial | Complete |
| Permanent Secrets | Common | Eliminated |
| Service Trust Scope | Broad | Minimal |
| Monitoring Coverage | Low | High |
| Machine-Driven Incidents | Rising | Reduced |
🧭 Leadership Takeaway
“Zero Trust collapses
when machines are trusted more than people.”
Boards must demand:
👉 Inventory of machine identities
👉 Rotation & expiry evidence
👉 Scope reduction metrics
👉 Monitoring of machine behavior
👉 Reduction in non-human attack paths
CISORadar converts machine trust into governed identity risk.
📩 Download
Non-Human Identity Audit Checklist + MTRI Scorecard
(ISO 27001 / NIST)
Available inside the CISORadar Cyber Authority Community.
🔖 SEO Tags
#AuditSecIntel #MachineIdentity #NonHumanIdentity #ServiceAccounts #CloudSecurity #ISO27001 #NISTAC2 #ZeroTrust #CISORadar #DigitalTrust