🧠 AuditSec Intel™ 1066 – “The Exception Debt Crisis: How ‘Temporary’ Access Exceptions Became Permanent Breach Paths in 2025”
🔍 Introduction — Nothing Is More Permanent Than Temporary
Every CISO has approved it:
“Just for now.”
“Business-critical.”
“We’ll remove it later.”
In 2025 breach reviews, CISORadar found the same root cause again and again:
Exception debt.
Controls were not bypassed once —
they were bypassed forever.
⚠️ 2025 Reality — Exceptions That Never Expired
| Exception Type | Original Reason | What Went Wrong | Impact |
|---|---|---|---|
| MFA bypass | VIP productivity | Never re-enabled | Account takeover |
| Firewall rule | Incident response | No expiry | Lateral movement |
| Admin access | Vendor support | No review | Ransomware |
| Logging disablement | Performance | Never restored | No detection |
| Encryption exception | Legacy system | Risk accepted once | Data breach |
CISORadar Insight:
“The breach didn’t break controls —
it walked through approved exceptions.”
🧩 Ignored Control: ISO 27001 A.5.37 / A.5.16 / NIST CM-3 — Security Exception Governance
| Control Area | Objective | Common Failure |
|---|---|---|
| Exception Registry | Track all exceptions | Informal approvals |
| Expiry | Auto-expire exceptions | Permanent bypass |
| Risk Acceptance | Document residual risk | No accountability |
| Approval Authority | Enforce senior sign-off | Rubber-stamping |
| Monitoring | Watch exception paths | Blind spots |
| Review Cycle | Revalidate necessity | Never reviewed |
💬 CISORadar Observation:
“Organizations governed controls —
but never governed the exceptions.”
🧠 CISORadar Control Test of the Week
Control Reference: ISO 27001 A.5.37 / NIST CM-3
Objective: Ensure exceptions don’t become invisible attack paths.
🔍 Test Steps
1️⃣ Inventory all approved security exceptions.
2️⃣ Identify exceptions without expiry dates.
3️⃣ Review approvals and risk acceptance evidence.
4️⃣ Validate monitoring on exception paths.
5️⃣ Test detection when exceptions are abused.
6️⃣ Check for duplicated or forgotten exceptions.
7️⃣ Simulate attacker use of an exception.
8️⃣ Calculate Exception Exposure Index (EEI).
🔎 Expected Outcomes
✅ Central exception register
✅ Mandatory expiry dates
✅ Senior risk ownership
✅ Continuous monitoring
✅ Reduced exception surface
Tools Suggested:
GRC Platforms | Change Mgmt | IAM | Firewall Mgmt | CISORadar Exception Risk Lens
🧨 Real Case: “Approved to Be Breached”
A firewall exception approved during an outage.
Never removed.
Attackers found it months later.
Loss: ₹1,120 Crore.
Lesson:
“If an attacker can’t break your controls,
they’ll wait for you to waive them.”
[Note – Fictitious for educational purposes only.]
🚀 CISORadar Impact Model – Exception Exposure Index (EEI)
| Metric | Before CISORadar | After CISORadar |
|---|---|---|
| Untracked Exceptions | Many | Zero |
| Expired Exceptions | Rare | Enforced |
| Exception Visibility | Low | High |
| Abuse Detection | Weak | Strong |
| Control Integrity | Eroded | Restored |
🧭 Leadership Takeaway
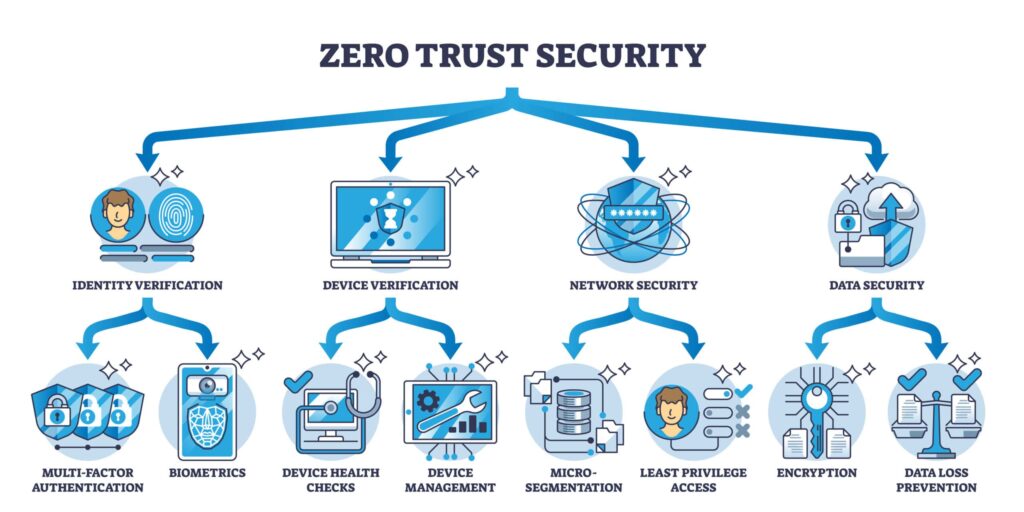
“Zero Trust collapses
when exceptions outlive the risk.”
Boards must demand:
👉 A live exception register
👉 Expiry & review metrics
👉 Monitoring of exception paths
👉 Ownership of accepted risk
👉 Reduction in exception count over time
CISORadar converts exception chaos into controlled, auditable risk.
📩 Download
Security Exception Governance Audit Checklist + EEI Scorecard
(ISO 27001 / NIST CM-3)
Available inside the CISORadar Cyber Authority Community.
🔖 SEO Tags
#AuditSecIntel #ExceptionManagement #ZeroTrust #ISO27001 #NISTCM3 #CyberRisk #CISORadar #DigitalTrust #SecurityGovernance #AuditIntelligence
Disclaimer: This post provides general information and is not tailored to any specific individual or entity. It includes only publicly available information for general awareness purposes. Do not warrant that this post is free from errors or omissions. Views are personal