🧠 AuditSec Intel™ 1063 – “The East-West Blind Spot: How Lateral Movement Made Breaches Inevitable in 2025”
🔍 Introduction — The Attack Didn’t Come From Outside
Most CISOs invested heavily in:
✔️ Firewalls
✔️ EDR
✔️ MFA
✔️ Zero Trust entry points
Yet in 2025 breach forensics, one fact stood out:
👉 The attacker entered once — and then moved freely inside.
No alarms.
No blocks.
No resistance.
CISORadar investigations confirmed:
East-West traffic became the attacker’s superpower.
⚠️ 2025 Breach Reality — One Entry, Many Compromises
| Initial Access | Internal Movement | Failure | Impact |
|---|---|---|---|
| Phished user | SMB & RDP | Flat internal network | Domain takeover |
| Vendor VPN | Service-to-service | No micro-segmentation | Ransomware |
| Cloud workload | API calls | Excessive trust | Data exfiltration |
| Container pod | East-west APIs | No visibility | Supply-chain breach |
CISORadar Insight:
“Perimeter security stopped intrusions —
but trusted traffic finished the breach.”
🧩 Ignored Control: ISO 27001 A.8.20 / A.8.21 / NIST AC-4, SC-7 — Internal Trust Boundaries
| Control Area | Objective | Common Failure |
|---|---|---|
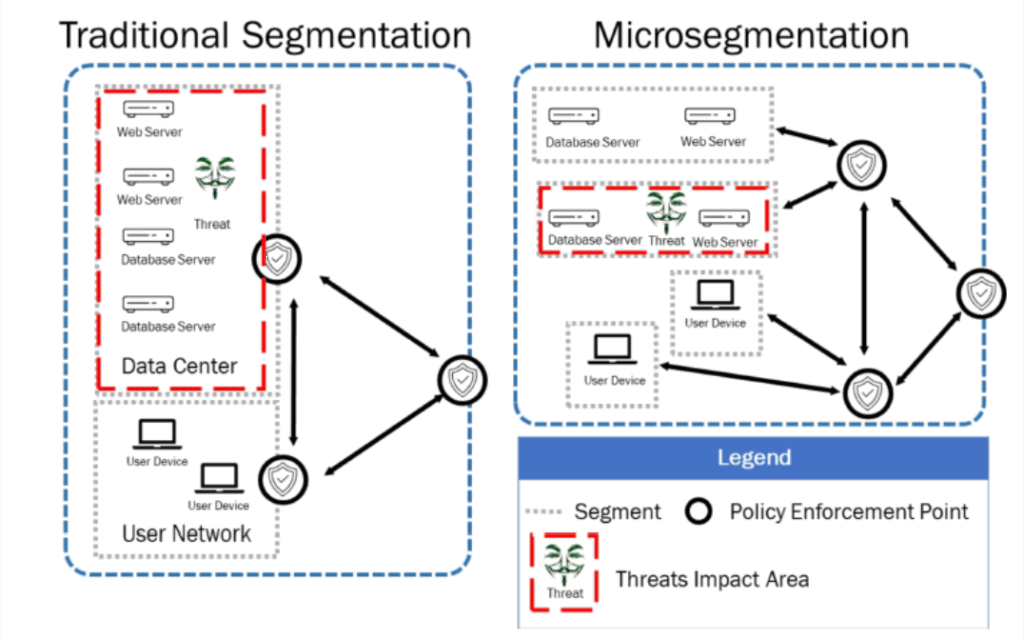
| Network Segmentation | Limit blast radius | Flat networks |
| East-West Monitoring | Detect lateral movement | North-south only |
| Service Identity | Verify internal calls | Implicit trust |
| Access Boundaries | Enforce least trust | Over-permissive |
| Logging | Track internal paths | Missing telemetry |
💬 CISORadar Observation:
“Organizations hardened the gate —
but left the hallways unlocked.”
🧠 CISORadar Control Test of the Week
Control Reference: ISO 27001 A.8.20 / NIST AC-4
Objective: Detect and contain lateral movement before it escalates.
🔍 Test Steps
1️⃣ Map all east-west traffic flows.
2️⃣ Identify flat trust zones.
3️⃣ Review internal service-to-service authentication.
4️⃣ Validate segmentation rules and enforcement.
5️⃣ Test lateral movement scenarios.
6️⃣ Review logs for unusual internal paths.
7️⃣ Simulate compromised workload movement.
8️⃣ Calculate Lateral Exposure Index (LEI).
🔎 Expected Outcomes
✅ Micro-segmentation enforced
✅ Internal identities verified
✅ East-west traffic logged
✅ Blast radius reduced
✅ Lateral movement detectable
Tools Suggested:
ZTNA | Micro-Segmentation | Service Mesh | Network Telemetry | CISORadar Trust Boundary Mapper
🧨 Real Case: The “Trusted Service” Breach
A compromised app server accessed:
✔️ Database
✔️ File shares
✔️ Backup systems
No alerts — because traffic was “internal”.
Loss: ₹3,400 Crore.
Lesson:
“Inside the network
is where attackers feel safest.”
[Note – Fictitious for educational purposes only.]
🚀 CISORadar Impact Model – Lateral Exposure Index (LEI)
| Metric | Before CISORadar | After CISORadar |
|---|---|---|
| Flat Trust Zones | Many | Eliminated |
| East-West Visibility | Low | High |
| Internal Auth | Implicit | Enforced |
| Blast Radius | Large | Minimal |
| Lateral Movement Risk | Critical | Controlled |
🧭 Leadership Takeaway
“Zero Trust fails
when internal traffic is never questioned.”
Boards must ask:
👉 How much internal traffic is monitored?
👉 Can one workload reach many systems?
👉 Is east-west movement logged and reviewed?
👉 What is our lateral blast radius?
CISORadar converts implicit trust into measurable boundaries.
📩 Download
Trust Boundary & Lateral Movement Audit Checklist + LEI Scorecard
(ISO 27001 / NIST AC-4)
Available inside the CISORadar Cyber Authority Community.
🔖 SEO Tags
#AuditSecIntel #LateralMovement #ZeroTrust #EastWestTraffic #ISO27001 #NISTAC4 #MicroSegmentation #CloudSecurity #CISORadar #DigitalTrust
Disclaimer: This post provides general information and is not tailored to any specific individual or entity. It includes only publicly available information for general awareness purposes. Do not warrant that this post is free from errors or omissions. Views are personal