🧠 AuditSec Intel™ 1058 – “The Backup Illusion: Why ‘Backups Exist’ Didn’t Mean ‘Recovery Was Possible’ in 2025”
🔍 Introduction — When Backups Gave False Confidence
In almost every ransomware tabletop exercise, one line is repeated:
“We’ll restore from backups.”
In 2025, breach investigations revealed a painful truth:
👉 Backups existed
👉 Backup jobs were “successful”
👉 Dashboards were green
Yet restoration failed when it mattered most.
CISORadar calls this: The Backup Illusion.
⚠️ 2025 Case Files — When Backups Failed at the Worst Moment
| Sector | Backup Status | Hidden Failure | Impact |
|---|---|---|---|
| BFSI | Daily backups green | Restore never tested | Multi-day outage |
| Healthcare | Encrypted backups | Keys stored with production | Data loss |
| SaaS | Cloud snapshots enabled | Snapshots deleted by attacker | Tenant shutdown |
| Manufacturing | Offline backups claimed | Media inaccessible | Plant downtime |
| Retail | DR backups available | RTO unrealistic | Revenue loss |
CISORadar Insight:
“Backups don’t protect data —
successful restores do.”
🧩 Ignored Control: ISO 27001 A.12.3.1 / NIST CP-9 — Backup Integrity & Recovery Readiness
| Control Area | Objective | Common Failure |
|---|---|---|
| Backup Integrity | Ensure backups are usable | No integrity validation |
| Restore Testing | Prove recovery works | Tests skipped |
| Credential Isolation | Protect backup admins | Shared credentials |
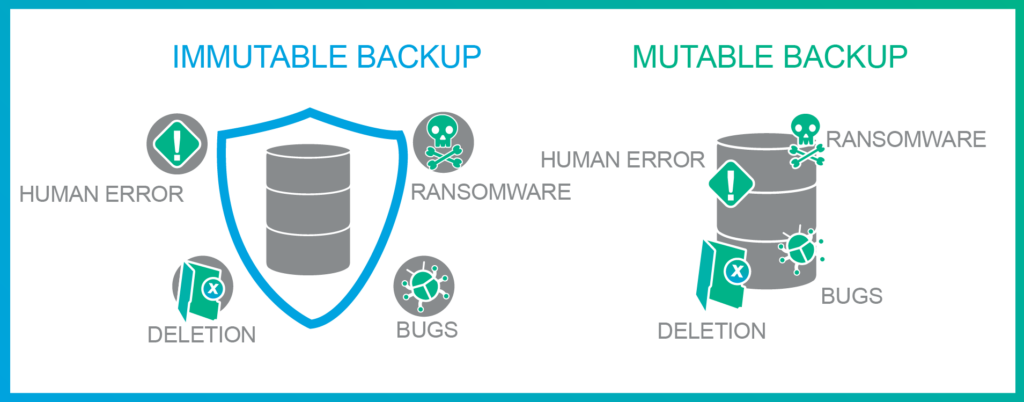
| Immutability | Prevent backup deletion | Soft-delete only |
| Key Management | Separate encryption keys | Keys compromised |
| RTO/RPO Reality | Align with business | Unrealistic assumptions |
💬 CISORadar Observation:
“Organizations backed up data —
but never backed up confidence in recovery.”
🧠 CISORadar Control Test of the Week
Control Reference: ISO 27001 A.12.3.1 / NIST CP-9
Objective: Validate real recovery capability — not backup existence.
🔍 Test Steps
1️⃣ Identify crown-jewel systems and datasets.
2️⃣ Validate last successful restore, not backup.
3️⃣ Test restoration without production credentials.
4️⃣ Attempt restore under ransomware simulation.
5️⃣ Validate immutable backup enforcement.
6️⃣ Measure actual RTO vs approved RTO.
7️⃣ Review key and credential separation.
8️⃣ Generate CISORadar Restore Readiness Index (RRI).
🔎 Expected Outcomes
✅ Restores proven, not assumed
✅ Backup credentials isolated
✅ Immutable backups enforced
✅ Keys protected and segregated
✅ RTO/RPO realistic
✅ Recovery confidence measurable
Tools Suggested:
Backup Platforms | Immutable Storage | Key Mgmt | DR Testing | CISORadar Recovery Assurance Matrix
🧨 Real Case: The Backup That Couldn’t Be Restored
A ransomware attack encrypted production.
Backups existed.
Dashboards were green.
Restoration failed due to:
- Corrupted backup chains
- Missing keys
- No tested runbook
Loss: ₹3,400 Crore.
Lesson:
“Backups without restore testing are insurance policies you never read.”
🚀 CISORadar Impact Model – Restore Readiness Index (RRI)
| Metric | Before CISORadar | After CISORadar |
|---|---|---|
| Restore Tests Passed | 0 | 100% |
| Backup Credential Isolation | Weak | Strong |
| Immutable Backup Coverage | Partial | Full |
| Actual RTO Achieved | Missed | Met |
| Recovery Confidence | Low | High |
🧭 Leadership Takeaway
“Resilience is not about having backups —
it is about proving recovery under attack.”
Boards must demand:
👉 Restore test evidence
👉 Immutable backup metrics
👉 Credential separation proof
👉 RTO reality checks
👉 Recovery assurance dashboards
CISORadar replaces backup optimism with verified cyber resilience.
📩 Download
Backup Integrity Audit Checklist + Restore Readiness Scorecard
(ISO 27001 A.12.3.1 / NIST CP-9)
Available inside the CISORadar Cyber Authority Community.
🔗 Join Now → CISORadar Cyber Authority Community
🔖 SEO Tags
#AuditSecIntel #BackupSecurity #CyberResilience #DisasterRecovery #ISO27001 #NISTCP9 #DigitalTrust #CISORadar #RansomwareDefense #BusinessContinuity