🧠 AuditSec Intel™ 1059 – “The East-West Blind Spot: How Internal Traffic Became the Stealthiest Breach Path in 2025”
🔍 Introduction — When the Perimeter Wasn’t the Problem
By 2025, most organizations confidently stated:
✅ Firewalls hardened
✅ Perimeter monitored
✅ North–south traffic inspected
Yet attackers didn’t fight the perimeter.
They entered once —
then moved freely inside, unseen.
CISORadar breach reviews uncovered a hard truth:
The most dangerous traffic never left the network — it moved laterally.
CISORadar calls this: The East-West Blind Spot.
⚠️ 2025 Case Files — How Lateral Movement Went Undetected
| Sector | Entry Point | Blind Spot | Impact |
|---|---|---|---|
| BFSI | Phished endpoint | No east–west inspection | Core banking access |
| Healthcare | Compromised IoT | Flat VLANs | PHI exposure |
| SaaS | Cloud workload breach | No microsegmentation | Tenant isolation failure |
| Manufacturing | OT jump host | Unmonitored internal flows | Plant disruption |
| Retail | Vendor VPN | Internal trust assumed | Data exfiltration |
CISORadar Insight:
“Attackers didn’t evade detection —
they moved where no one was looking.”
🧩 Ignored Control: ISO 27001 A.8.20 / A.8.21 / NIST SC-7, AC-4 — Internal Network Segmentation & Monitoring
| Control Area | Objective | Common Failure |
|---|---|---|
| East-West Visibility | Inspect lateral traffic | Only perimeter logs |
| Segmentation | Limit internal trust | Flat networks |
| Service Trust | Authenticate internal services | IP-based trust |
| Workload Identity | Verify machine-to-machine access | No identity checks |
| OT/IoT Segregation | Isolate sensitive zones | Shared networks |
| Internal Detection | Detect lateral movement | No baselining |
💬 CISORadar Observation:
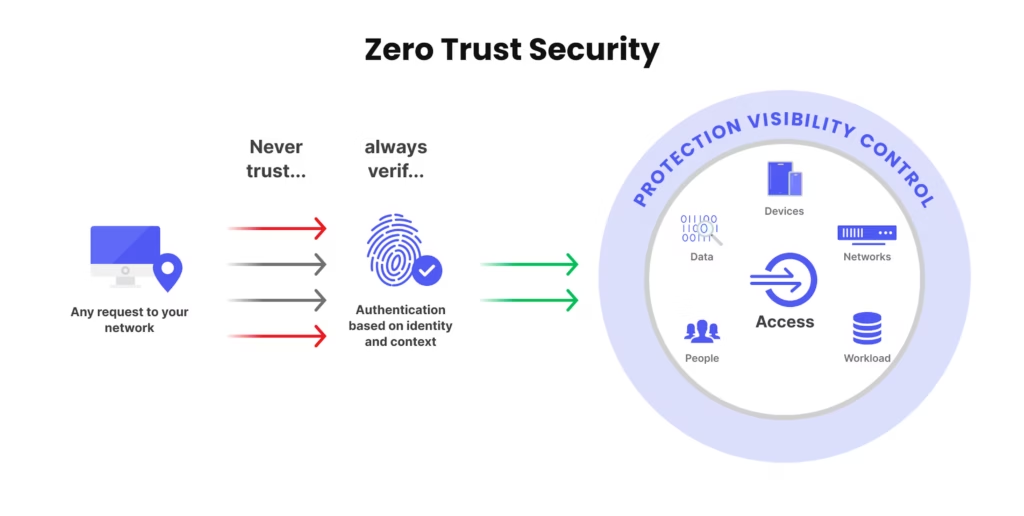
“Zero Trust at the edge means nothing
if trust is infinite inside.”
🧠 CISORadar Control Test of the Week
Control Reference: ISO 27001 A.8.20 / NIST SC-7
Objective: Expose hidden lateral movement paths.
🔍 Test Steps
1️⃣ Map internal network zones and trust boundaries.
2️⃣ Identify systems communicating without authentication.
3️⃣ Review east–west traffic logging coverage.
4️⃣ Detect unencrypted internal protocols.
5️⃣ Validate microsegmentation enforcement.
6️⃣ Simulate attacker lateral movement.
7️⃣ Review OT/IoT internal access paths.
8️⃣ Generate CISORadar Lateral Exposure Index (LEI).
🔎 Expected Outcomes
✅ East–west traffic visible
✅ Internal trust minimized
✅ Segmentation enforced
✅ Lateral movement alerts triggered
✅ Internal attack paths reduced
Tools Suggested:
NDR | Microsegmentation | ZTNA | Service Mesh | CISORadar Trust Boundary Mapper
🧨 Real Case: “Inside Was Trusted”
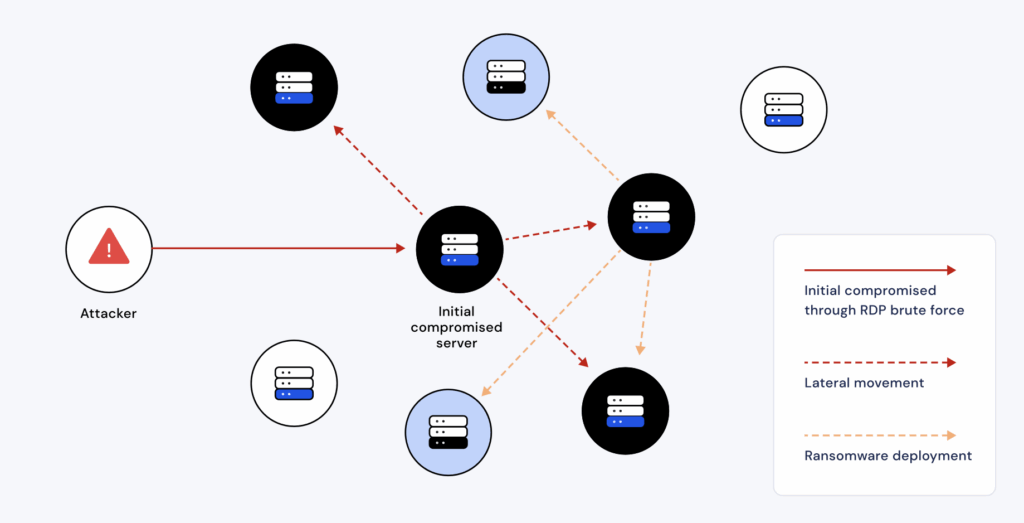
Attackers compromised one internal server.
No alerts fired —
because traffic stayed inside.
They laterally accessed 47 systems before detection.
Loss: ₹2,750 Crore.
Lesson:
“The breach didn’t spread fast —
it spread silently.”
🚀 CISORadar Impact Model – Lateral Exposure Index (LEI)
| Metric | Before CISORadar | After CISORadar |
|---|---|---|
| East-West Visibility | Low | High |
| Flat Network Zones | Many | Minimal |
| Unauthenticated Services | Common | Rare |
| Lateral Dwell Time | Weeks | Hours |
| Internal Attack Paths | Numerous | Limited |
🧭 Leadership Takeaway
“Zero Trust is not a perimeter strategy —
it is an internal discipline.”
Boards must demand:
👉 East-west traffic visibility
👉 Internal segmentation metrics
👉 Lateral movement testing results
👉 Trust boundary enforcement evidence
👉 Reduced internal blast radius
CISORadar turns internal invisibility into measurable digital trust.
📩 Download
Trust Boundary & Lateral Movement Audit Checklist + LEI Scorecard
(ISO 27001 / NIST SC-7)
Available inside the CISORadar Cyber Authority Community.
🔗 Join Now → CISORadar Cyber Authority Community
🔖 SEO Tags
#AuditSecIntel #EastWestTraffic #LateralMovement #ZeroTrust #NetworkSegmentation #ISO27001 #NISTSC7 #CISORadar #DigitalTrust #CyberResilience