Here’s your next flagship intelligence post for CISORadar.com – AuditSec Intel™ #1009, continuing the “One Control a Day – One Breach Prevented” mission.
This edition focuses on one of the most overlooked controls in the AI-powered enterprise era — Asset Inventory & Visibility, the first pillar of Zero Trust and digital trust building.
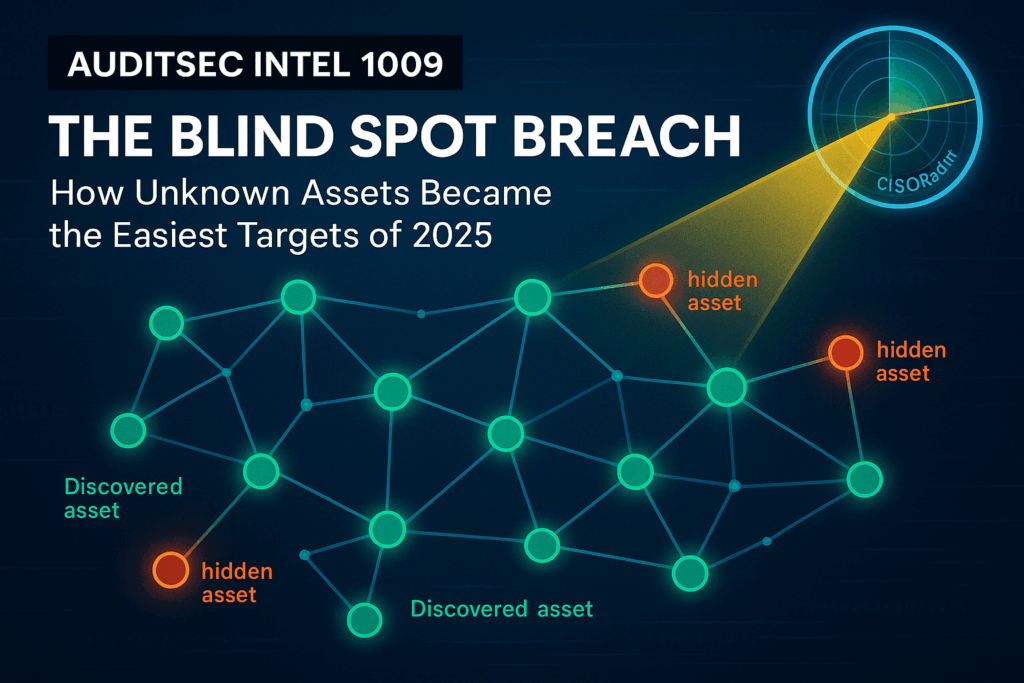
🛰️ AuditSec Intel 1009 – The Blind Spot Breach: How Unknown Assets Became the Easiest Targets of 2025
💻 Introduction: You Can’t Protect What You Don’t Know Exists
In 2025, as organizations raced toward automation and AI integration, one foundational truth was forgotten —
“Visibility isn’t optional. It’s your first defense.”
Attackers no longer need to bypass advanced defenses; they simply find unmonitored devices, untagged cloud instances, or untracked shadow systems.
And those blind spots became breach entry points for hundreds of organizations this year.
⚠️ The 2025 Asset Blind Spot Statistics
Based on the CISORadar Threat Intelligence Index (Q3 2025):
| Category | Breach Cause | Example | Frequency |
|---|---|---|---|
| Shadow IT & unmanaged SaaS | Users connecting personal apps to corporate email | Cloud credential exposure | 33% |
| Forgotten cloud instances | Unpatched EC2 and Azure VMs left running | Crypto mining & data leaks | 29% |
| Untracked IoT/OT devices | Factory or hospital systems unmonitored | Malware lateral spread | 21% |
| Legacy systems outside EDR | Obsolete OS, no monitoring agent | Exploited by botnets | 17% |
💡 Insight:
“Every untagged asset is a future incident report waiting to happen.”
🧩 Ignored Control: ISO 27001 A.8.1.1 / NIST CM-8 – Asset Inventory & Ownership
| Area | Objective | Common Gap |
|---|---|---|
| Asset Register | Maintain inventory of all information assets | Static spreadsheets, outdated data |
| Asset Ownership | Assign accountable owner for each asset | No ownership mapping |
| Automated Discovery | Continuous detection of devices and cloud assets | Manual, not real-time |
| Classification | Tag assets by criticality and business impact | Inconsistent, missing tags |
💡 CISORadar Insight:
71% of organizations discovered 10–30% more assets after implementing automated discovery.
🧠 CISORadar Control Test of the Week
Control Reference: ISO 27001 A.8.1.1 / NIST CM-8
Objective: Ensure all physical, virtual, and cloud assets are identified, owned, and continuously monitored.
Test Steps:
1️⃣ Collect inventory from ITSM, CMDB, and cloud portals.
2️⃣ Compare against network scan or discovery tool output.
3️⃣ Identify discrepancies > 5%.
4️⃣ Verify ownership assigned for each high-risk asset.
5️⃣ Validate tagging consistency (critical, confidential, public).
Expected Results:
✅ 100% critical assets tracked
✅ Ownership assigned and documented
✅ Discrepancy gap < 5%
Tools Suggested:
Lansweeper | Qualys Global AssetView | ServiceNow CMDB | CISORadar Asset Visibility Template
🔥 Case Study: The 2025 FinTech Shadow API Breach
Scenario:
A FinTech startup hosted test APIs on a dev cloud account created by a contractor.
No one knew it existed post-project.
Attackers found the endpoint, accessed a production database clone, and exfiltrated 1.3M user records.
Impact:
- 1.3M customer data records leaked
- ₹90 Cr loss and regulatory fines
- SOC never received alerts — asset unmonitored
Audit Finding:
Asset policy defined ✅
Continuous discovery ❌
Ownership mapping ❌
Lesson:
“You can’t defend a ghost. Unseen assets are unprotected assets.”
🚀 CISORadar ROI Model – Asset Visibility Index (AVI)
| Metric | Before CISORadar Control Test | After Implementation |
|---|---|---|
| Untracked Assets | 18% | < 3% |
| Detection Time (Unknown Device) | 45 Days | 4 Hours |
| Incident Rate per 100 Devices | 11 | 2 |
| Audit Readiness Score | 62% | 94% |
🧭 Leadership Takeaway
“Every secure enterprise starts with knowing its digital map.”
Boards should make “100% Asset Visibility” a mandatory KPI — because what isn’t seen, can’t be secured.
📩 Download the “Asset Visibility Audit Template (A.8.1.1 / NIST CM-8)”
🎯 Join the CISORadar Cyber Authority WhatsApp Group to access:
📘 “Asset Register + Ownership Mapping Template (A.8.1.1 / NIST CM-8)”
🔗 Join Now → CISORadar Cyber Authority Community
📣 Share this with your IT, Cloud, and Audit teams — because asset visibility is where cybersecurity maturity begins.
🔖 Tags & SEO Keywords:
#AuditSecIntel #AssetInventory #ISO27001A811 #NISTCM8 #CISORadar #ZeroTrust #DigitalTrust #ShadowIT #CyberVisibility #CISO2 #AITrustAudits, Cybersecurity in AI Era, AI Cybersecurity, ISO 27001 Implementation, ISO 27001 Certification